This is the third video that will demonstrate how to use the Saint Penetration Tool and Windows Command Line to Cover Your Tracks by deleting Event Viewer files and deleting the administrative user that you created.
0Related Posts

CISA assesses that the United States and European nations may experience disruptive and defacement attacks against websites in an attempt…
0
Topgallant Partners was recently Certified by New York as a New York State Certified Service-Disabled Veteran Owned Business. Topgallant Received the news in April. The news was received in a letter written by the Executive Director for Division of Service-Disabled Veterans’ Business Development, Kenneth E. Williams.
1
The Justice Department announced today a disruption campaign against the Blackcat ransomware group — also known as ALPHV or Noberus…
0
May 2023 Newsletter Tim Cook Said Recently “In The World of Cybersecurity The Last Thing You Want Is To Have…
0
Microsoft Zero Day Vulnerability/Exploit Follina Found A Zero-Day Vulnerability/Exploit “Follina” has been found in Microsoft Office and Microsoft Windows…
0
Have you ever wondered what a Salted Hash was? Well, here is the Cliff Notes’ Version Hashing is a function…
0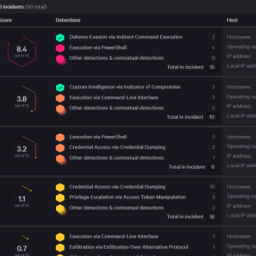
Introduction In the quest to strengthen cybersecurity defenses, organizations have turned to various solutions such as SIEM, XDR/MDR, and SOAR….
0
Healthcare spending in the U.S. — which is the highest among developed countries — accounts for 18 percent of the…
0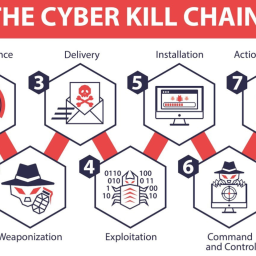
What is the Mitre ATT&CK Framework? The Mitre ATT&CK Framework describes the techniques, tactics and procedures that hackers use to…
1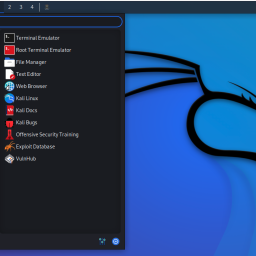
Seemingly Benign Programs used for Hacking Hackers use seemingly benign programs for Nefarious Purposes. Hackers manipulate and repurpose software and…
1
The Cyber Security and Infrastructure Security Agency (CISA) has come to the rescue for those affected by a Recent Ransomware…
0Hi All, In my last Video Demo, I exploited the Default SNMP String on a Cisco Router and gained access…
0
Introduction: Ransomware has become a prevalent and damaging threat in the world of cybersecurity. This malicious software aims to encrypt…
1
To help businesses uncover and fix the vulnerabilities and misconfigurations affecting their systems, there is an abundance of solutions available….
0
What is Cyber Insurance? Cyber Insurance is a type of insurance that helps businesses and individuals mitigate the financial losses…
0
