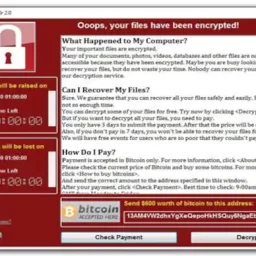
September 8, 2021 – Microsoft has discovered a remote code execution vulnerability in MSHTML that affects Microsoft Windows. The Vulnerability has been assigned a CVSS rating of 8.8 and assigned by MITRE as CVE-2021-40444. The Vulnerability Alert was issued yesterday.
Microsoft is aware of targeted attacks that attempt to exploit this vulnerability by using “specially-crafted” Microsoft Office documents. The Hack works like this.
- An attacker could craft a malicious ActiveX control to be used by a Microsoft Office document that hosts the browser rendering engine.
- The attacker would then have to convince the user to open the malicious document. Using either a website with the Hack File embedded or attached to a an email.
According to Microsoft, “Users whose accounts are configured to have fewer user rights on the system could be less impacted than users who operate with administrative user rights.” This is known as the concept of Least Privilege or providing the user only enough access to perform their tasks.
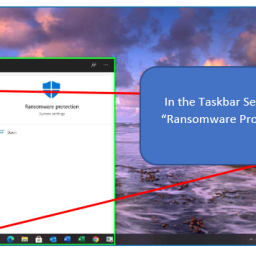
Microsoft Defender Antivirus and Microsoft Defender for Endpoint both provide detection and protections for the known vulnerability.
Customers should keep antimalware products up to date. Customers who utilize automatic updates do not need to take additional action.
Enterprise customers who manage updates should select the detection build 1.349.22.0 or newer and deploy it across their environments. Microsoft Defender for Endpoint alerts will be displayed as: “Suspicious Cpl File Execution”.
Mitigations
By default, Microsoft Office opens documents from the internet in Protected View or Application Guard for Office both of which prevent the current attack.
Workarounds
Disabling the installation of all ActiveX controls in Internet Explorer mitigates this attack. This can be accomplished for all sites by updating the registry. Previously installed ActiveX controls continued to run, but do not expose this vulnerability.
Please follow the link for Specific Guidance Here
1