This is the third video that will demonstrate how to use the Saint Penetration Tool and Windows Command Line to Cover Your Tracks by deleting Event Viewer files and deleting the administrative user that you created.
0Jeff has a M.A. in Computer Resources Management from Webster University and a B.A. in Journalism from Purdue University. He is a terrible golfer.
Related Posts

Topgallant Partners was recently Certified by New York as a New York State Certified Service-Disabled Veteran Owned Business. Topgallant Received the news in April. The news was received in a letter written by the Executive Director for Division of Service-Disabled Veterans’ Business Development, Kenneth E. Williams.
1
Washington, DC – Today, CISA, the Federal Bureau of Investigation (FBI), Europol’s European Cybercrime Centre (EC3), and the Netherlands’ National…
0
The Justice Department announced today a disruption campaign against the Blackcat ransomware group — also known as ALPHV or Noberus…
0
What is Cyber Insurance? Cyber Insurance is a type of insurance that helps businesses and individuals mitigate the financial losses…
0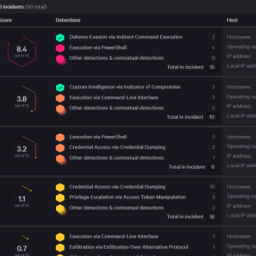
Introduction In the quest to strengthen cybersecurity defenses, organizations have turned to various solutions such as SIEM, XDR/MDR, and SOAR….
0
In a universe (not so far away), where passwords like “123456” and “password” reigned supreme, our hero, NIST 800-63B, stepped…
2
Seemingly Benign Programs used for Hacking Hackers use seemingly benign programs for Nefarious Purposes. Hackers manipulate and repurpose software and…
1September 19, 2012 Well, It looks like the HIPAA Enforcement Boys and Girls are getting serious. Mass Eye and Ear…
0
Healthcare spending in the U.S. — which is the highest among developed countries — accounts for 18 percent of the…
0
In the constantly evolving landscape of cloud computing, ensuring robust security measures is paramount. Recently, cybersecurity researchers have identified a…
0
May 2023 Newsletter Tim Cook Said Recently “In The World of Cybersecurity The Last Thing You Want Is To Have…
0
HealthEC LLC a New Jersey based health technology company reported a data breach that impacted nearly 4.5 million patients across…
0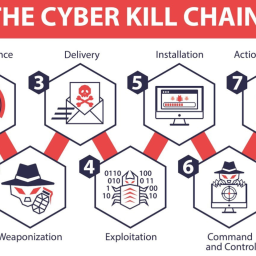
What is the Mitre ATT&CK Framework? The Mitre ATT&CK Framework describes the techniques, tactics and procedures that hackers use to…
1
Have you ever wondered what a Salted Hash was? Well, here is the Cliff Notes’ Version Hashing is a function…
0
Introduction: Ransomware has become a prevalent and damaging threat in the world of cybersecurity. This malicious software aims to encrypt…
1
